SENDES II C2
C-UAS command and control for defense and critical infrastructure, with coordinated detection, identification, and drone neutralization.
ASDT International operational presence
Global deployment of C-UAS installations.
Number of devices
deployed devices
Operational detection and neutralization network.
Flights
registered flights
107,028 classified as illegal to trigger coordinated response.
Operational coverage
protected sectors
Applied in sovereignty, critical infrastructure, operations, and events with organization-exclusive data.
Multiregional operational coverage with private per-client deployments
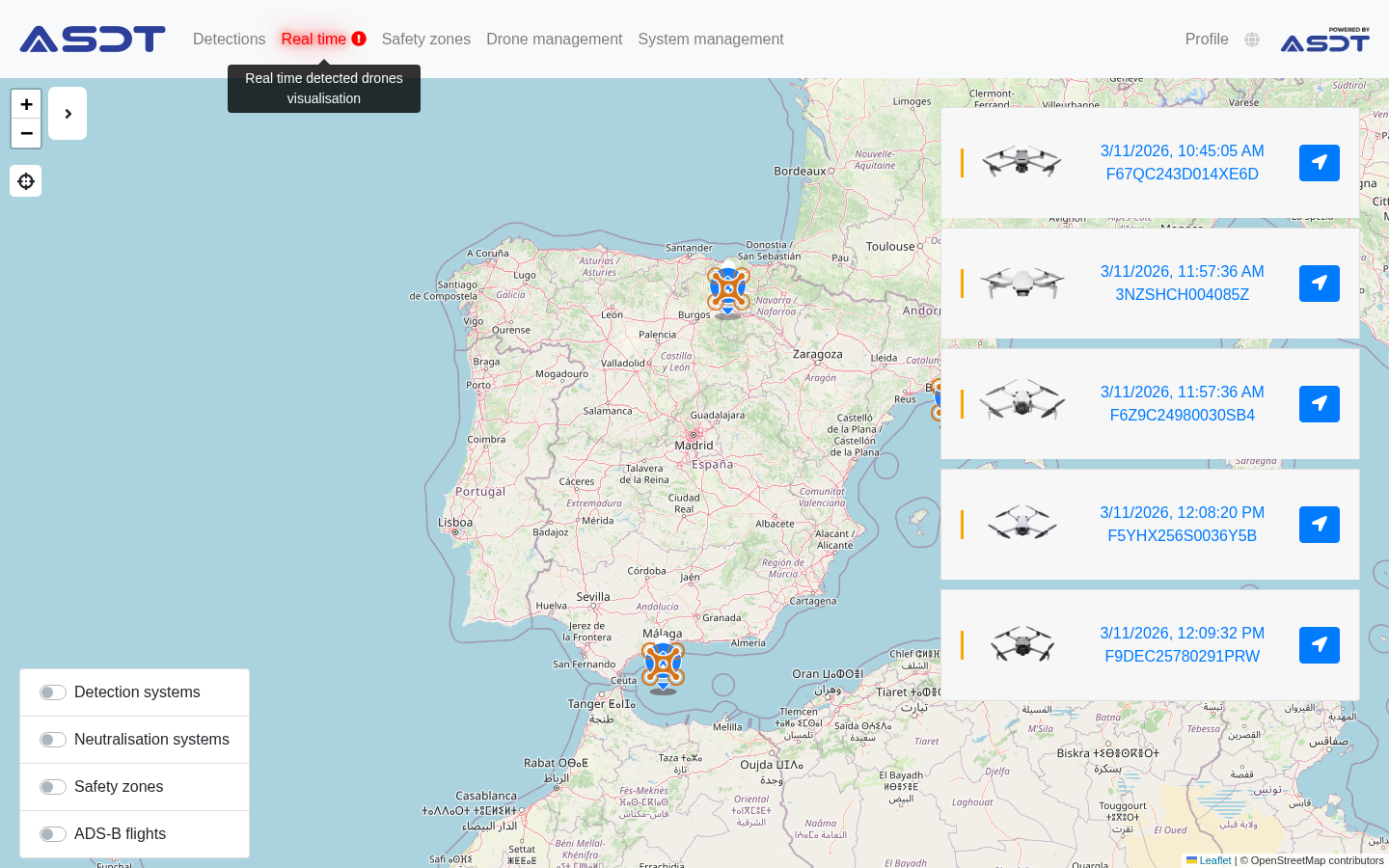
See the improvement in seconds
Select a view in the tabs and slide to compare SENDES I with SENDES II.
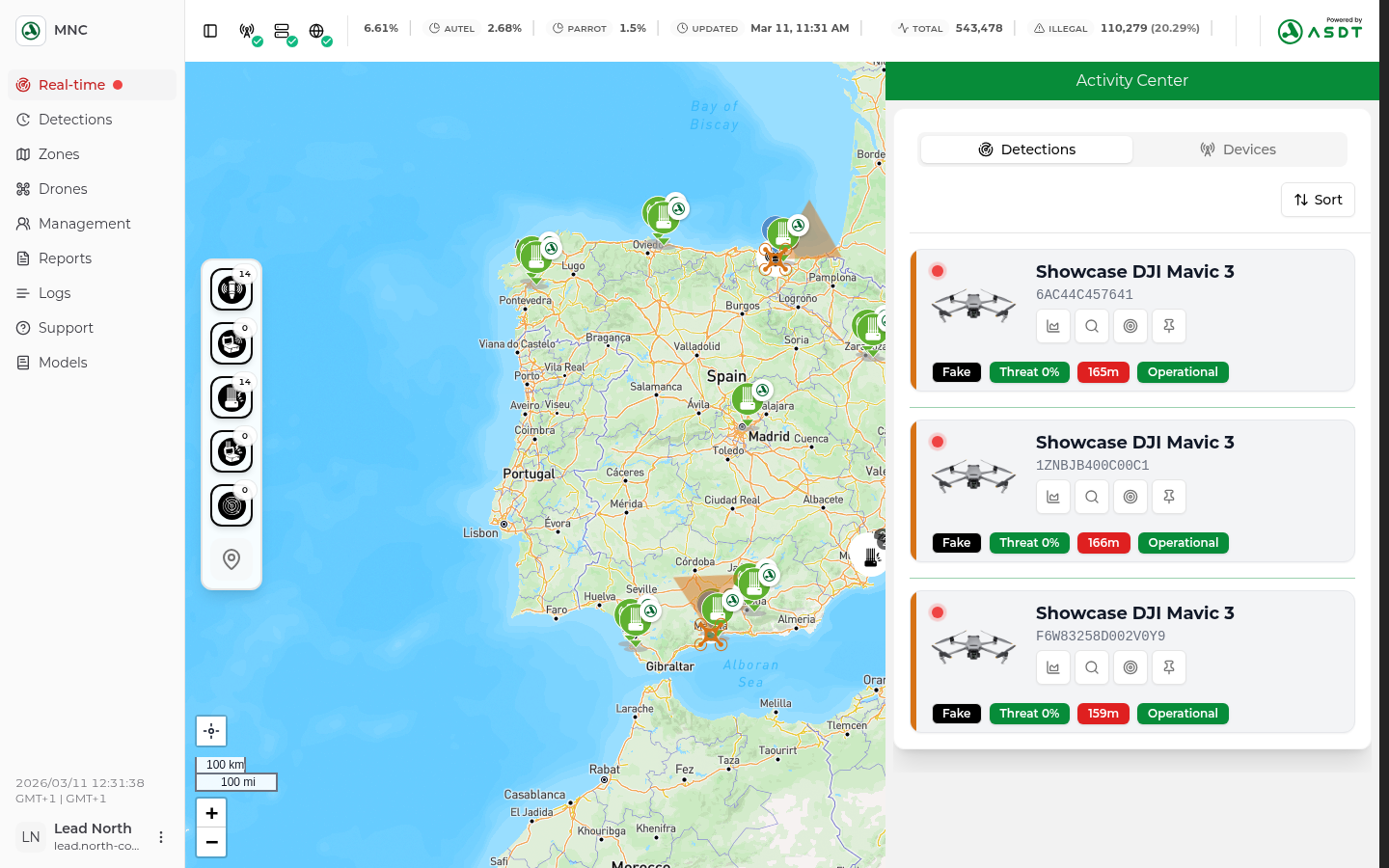
Real-time operation
The main view lets you visualize and act in real time on all drones and devices, see detections instantly, and execute neutralization in case of threat.
Slide to compare. Tap, hold, and move the divider. Use the arrow keys on desktop.
Tap, hold, and move the divider
What changes in this view
Each view focuses on a different area of the interface so the comparison is clearer even with the current screenshots.
- Access to real-time operational data and telemetry is more direct.
- Critical information and detections are located and understood faster.
- Interaction with the system requires fewer steps to go from analysis to action.
- Access to drones and devices for supervision and response is faster.
Product on screen
See a SENDES II preview before requesting a demo.

The full SENDES II operation is presented in private sessions focused on isolated environments, dedicated servers, and exclusive client data.
- Real-time operations center
- Isolated architecture with dedicated server per organization
- Group, user, and ZEVO zone administration
- Drone view, alert, and operational context
- Traceability and evidence for audit
Product screens
Operational capabilities
Features designed for critical environments where detection, response, isolation, and traceability cannot fail.
Isolated environment and sovereign data
Deployment in an isolated environment with a dedicated server or segregated instance so each client preserves full ownership, control, and separation of its information.
Zones with automated response
Define areas, rules, and thresholds to trigger automated actions during an incident, including automatic neutralization when procedure and applicable regulation allow it.
Configurable multichannel alerts
Push notifications on mobile, SMS, and email can be configured by role, severity, zone, or event type to alert only those who need to act at each moment.
Neutralization reports
Generate clear reports for each intervention with time, area, incident, executed response, and associated evidence to ease follow-up and later justification.
Audit and logs for the user
The client has audit and system logs to review access, changes, executed actions, and full operation traceability.
Analytics and business intelligence
Cross historical and operational data to detect patterns, compare periods, measure performance, and turn information into better-grounded decisions.
AI for threat and false flights
Advanced models help score threats, detect false flights, reduce operational noise, and prioritize incidents that truly require response.
Reinforced security
Hardened architecture with MFA, granular permissions, client segregation, encryption in transit and at rest, and access controls designed for sensitive environments.
Isolated C2 flow
Supports isolated deployments with no internet dependency.
Integrated sources
Radars
RF detectors
Cameras
Third-party APIs
SENDES II
Fusion, rules, traceability, and orchestration in an isolated environment
Users and effectors
C2 users
Mobile devices
Client dedicated server
Jammers
NATO interoperability with custom connectors
Ready integrations and custom adapters
SENDES II integrates protocols such as ASTERIX and SAPIENT, and adapts to existing tools such as ATAK, Active Directory, and third-party platforms.
Integration core
Connect protocols, users, and third parties without breaking operations.
Recent validations and cases
News and success cases published by ASDT and third parties.
Roadmap
From Q2 to Q4 of 2026. First deployments before 2027.
Q2 2026
Presale
Priority reservation for clients who want to influence integrations and C2 workflows.
In progressQ3 2026
Early access
First on-field deployments (in beta phase) with clients.
NextQ4 2026
Official launch
Commercial release of SENDES II, with intial deployments and migrations.
NextRequest a SENDES II proposal
Try SENDES II and get a quote specialized on your infrastructure and needs. Get a special deal during presale!
Includes a 1-year warranty and an implementation focused on isolated environments, dedicated servers, and exclusive information control.
Replies are sent by email, and the next conversation is coordinated with the ASDT team.